The Company Poddar Professional Solutions Pvt. Ltd. is managed by professionals like Chartered Accountants and Company Secretaries. It is professionally committed to provide dedicated service in a cost effective manner without diluting the quality.
Our strengths lie in the untiring hardwork of our dedicated teams, the healthy balance of our product and client mix and the long-standing relations with our clients.
The company provides services relating to Digital Signature, Various online filing like VAT eFiling, ITR eFiling, ROC eFiling, eTendering, Company Formation, Accounts and Audit and related Activities.
Digital Signature
markets, buyers search online for info
rather than talking.
For more information click here
e-Tendering
For more information click here
e-Filing
For more information click here
Document Signer
For more information click here
DGFT
For more information click here
Download
For more information click here
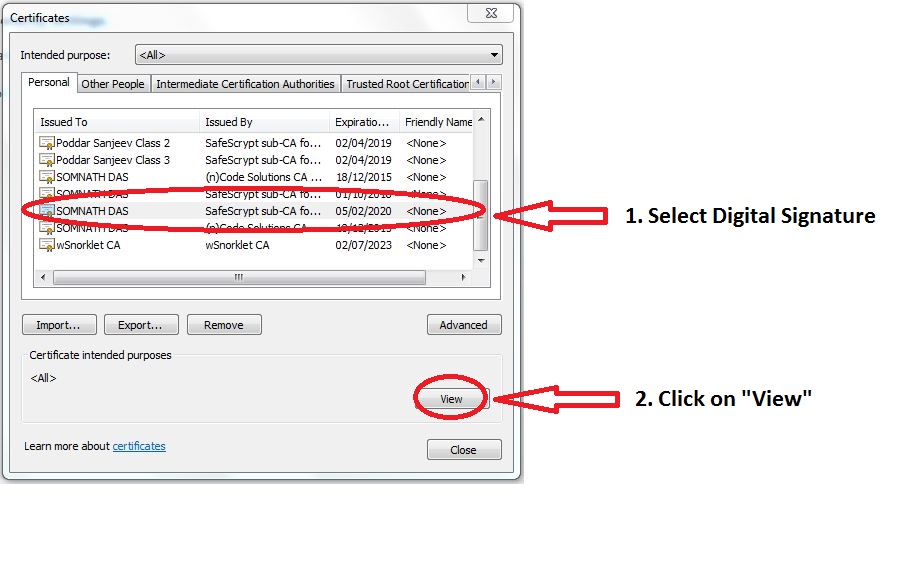
- Name and Expiry Date can be seen
- Select View and you can browse through different pages (1) General, (2) Details and (3) Certificate Path to see the various details of Digital Signature. Major items to be noticed are
- In General Page you will notice “You have a private key that corresponds to this Certificate”
- In Details page go to “Valid to” and see the time up to which your Digital Signature is Valid
- In Certificate Path see the following details






When you cancel an earlier communication you can get it back, but how does this work in environment?
Digital Signature
Digital signatures, a form of electronic signatures, are created and verified using...
20but friends.



Get in Touch
Office
13, B. B. Ganguly Street, (Near Lal bazaar, Opposite Himalaya Opticals)
Punar Nava Building, Ground Floor, Room No. 7, Kolkata-700012.
Say hello
Tel : (033) 4003 1162, (033) 4008 5487
Mob. : (+91) 99030 22336